How to assign Application Impersonation using Exchange Admin Console
If you are using Basic authentication to integrate your Microsoft Exchange with the AskCody Platform it requires Application Impersonation assigned. This article explains how to set it up using the Exchange Admin Console.
Why is Application Impersonation needed?
Application Impersonation is used to access appointments and monitor room calendars for changes; delegated access is not sufficient.
This article will guide you through the process of assigning application impersonation to the service account using the Office 365 Admin Management Console.
Assigning the application impersonation role from the Office 365 Admin Management Console.
Follow these steps to assign the application impersonation role from the Office 365 Admin Management Console.
Before you begin, you must have created an AskCody account in Exchange 2013 or Exchange Online, e.g. askcody@yourdomain.com, and changed the account’s temporary password to a permanent one.
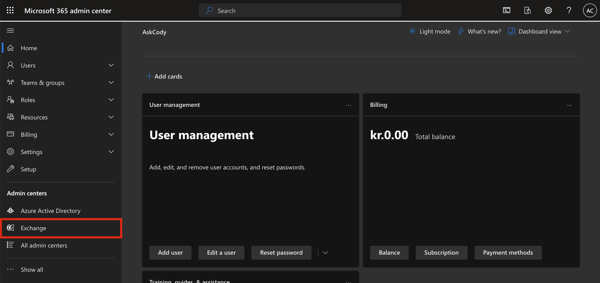
From the left panel in the Microsoft Admin Center, select Exchange in the list of items under "Admin Centers".
This will take you to the Exchange Admin Center. In here, select Permissions and under the Admins Roles, click the plus “+” sign and enter the Name and Description, e.g. ApplicationImpersonation.
Leave Default as the scope to apply the new role for the whole organization.
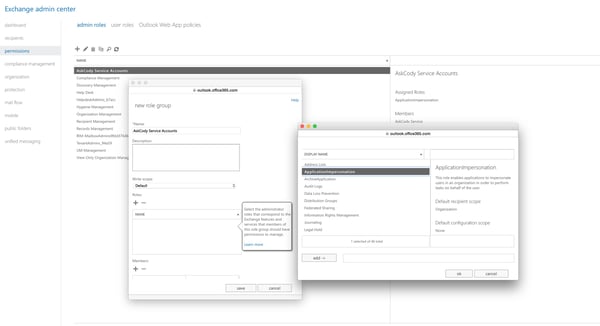
Then choose 'ApplicationImpersonation' from the list of roles.
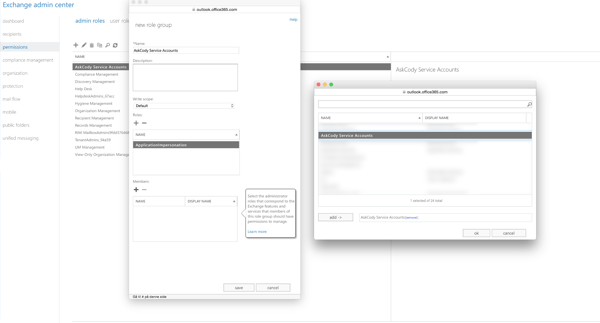
The next step is to select the users to whom this role will be assigned. In the example below, the user with the name AskCody Service Accounts is selected.
Confirm this selection by clicking Save and then allow some time for the system to implement this role.
Learn More
Go to Office Dev Center to learn more about using apps for Outlook for your organization
(Redirecting you to Microsoft Dev Center )
Disclaimer:
Despite the continued efforts of AskCody to ensure that the information in this document is as complete and up-to-date as possible, AskCody cannot be held accountable for the correctness and/or completeness and/or specific applicability of the published and/or requested information in this document. AskCody shall not be liable for any direct, indirect, incidental, special, or consequential damages, lost profits or business interruptions arising out of the use of this document. The extraction and use of information from this document remain at all times completely within the user's own risk.
![Logo - Secondary White-1.png]](https://help.askcody.com/hs-fs/hubfs/Logo%20-%20Secondary%20White-1.png?height=50&name=Logo%20-%20Secondary%20White-1.png)