Create a service account using the Exchange Admin Center (2013/2016)
Learn how to create a service account in your organization's Exchange Environment using the Exchange Admin Center graphic interface
The steps below will use screenshots from the Office 365 Admin Center and the Exchange Admin Center
The procedure is the same across all versions of Exchange, but the exact method might vary slightly.
*In order to integrate with Exchange Server using Basic Authentication, you must be a Global Administrator in your organization's Azure Active Directory.
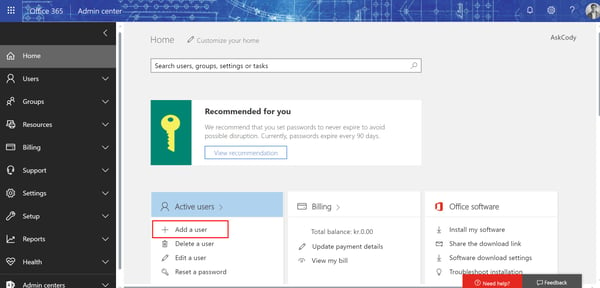
- Go to the Office 365 Admin Center and click Add a user
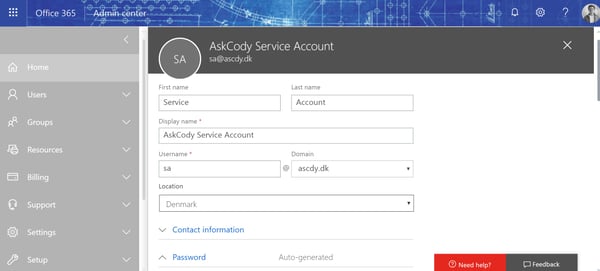
- Fill in the user information and select the same domain as your resource calendars are using
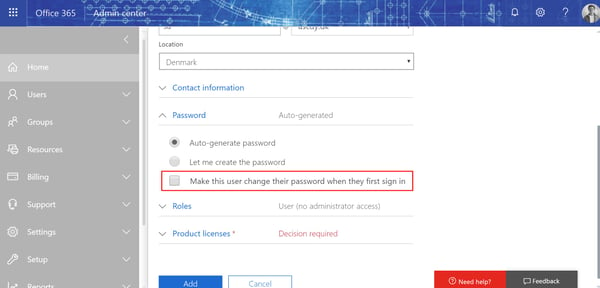
- Create a password and make sure that the checkbox Make the user change their password when the first sign in is NOT checked.
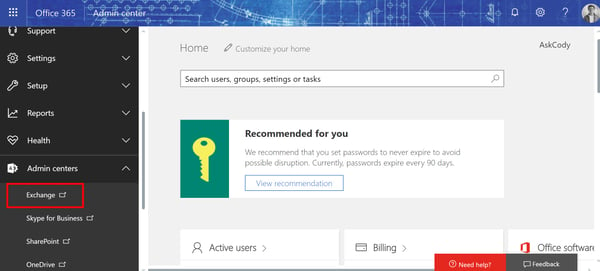
- Go to the Office 365 Admin Center, click Admin Centers, and select Exchange
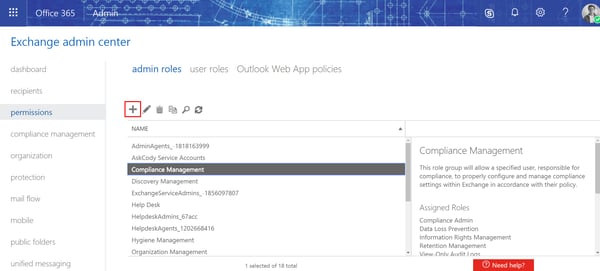
- Go to permissions and click the "+" icon to create a new role group
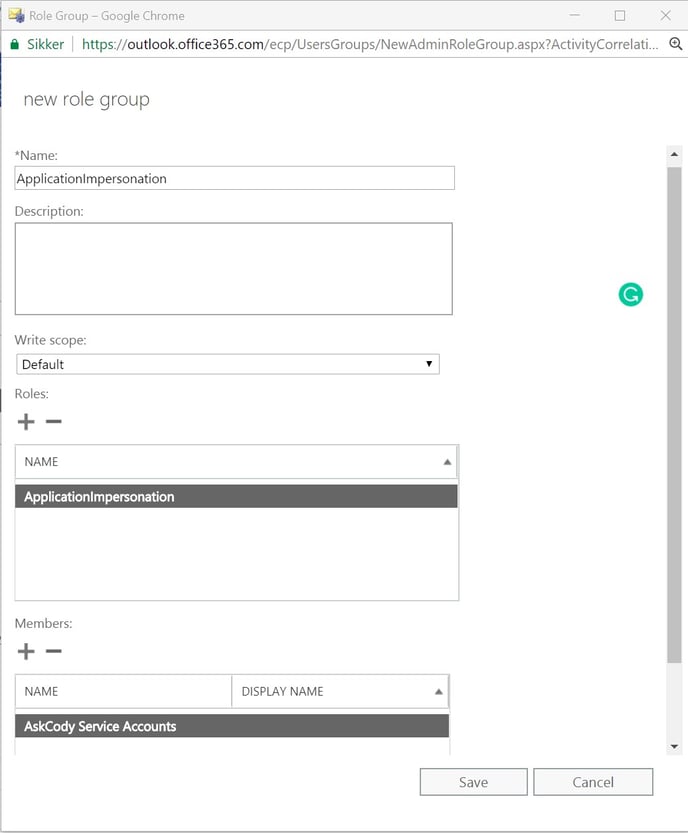
- Give the role group a name, click the "+" icon under Roles to add the ApplicationImpersonation role, and click the "+" icon under Members to add the Service Account to the role group. Click save to finish the role group.
-
Make sure that the Service Account is located in the same Exchange tenant/server as your resource calendars
In order for the Service Account to have access to your resource calendars, it is important that both the Service Account and the resource calendars are located on the same Exchange tenant/server.
If you have done exactly as shown in the previous steps there is no need to check if this is the case, as long as you can manage the resource calendars from the Office 365 Admin Center.
However, if you have created the Service Account using another method, please make sure that your Service Account is using the same domain as the resource calendars.
![Logo - Secondary White-1.png]](https://help.askcody.com/hs-fs/hubfs/Logo%20-%20Secondary%20White-1.png?height=50&name=Logo%20-%20Secondary%20White-1.png)